Trojan:Android/Pincer.A
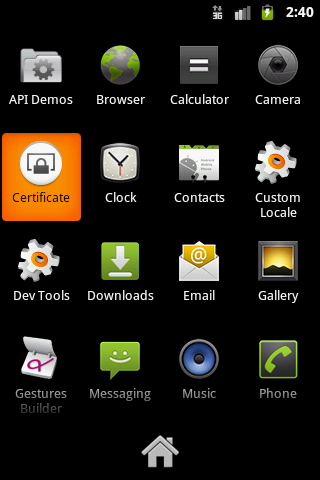
Protip: don’t install an Android application package file if it’s named “Certificate.apk”.
It’s not legit (obviously).
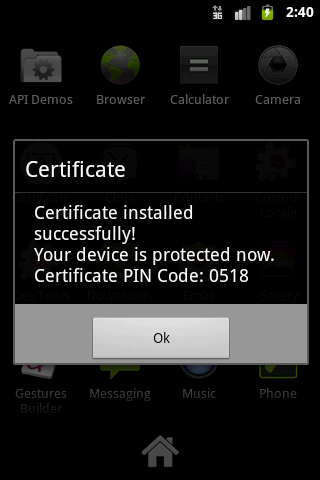
Trojan:Android/Pincer.A is able to forward SMS messages and perform other actions based on commands it receives from its C&C. When installed, it will appear in the application menu as “Certificate” and will display related bogus messages when run.
Previous malicious mobile applications pretending to be certificates have been mobile components of banking trojans aimed at defeating two-factor authentication. The fact Pincer is able to forward SMS messages means it can certainly also be used as such.
The commands Pincer waits for are:
• start_sms_forwarding
• start_call_blocking
• stop_sms_forwarding
• stop_call_blocking
• send_sms
• execute_ussd
• simple_execute_ussd
• stop_program
• show_message
• delay_change
• ping
The show_message command enables interesting interactivity as it displays a message to the victim, the message content comes from the C&C at the same time as the command itself is delivered.
The call-home destinations for the trojan are http://198.xxx.xxx.xxx:9081/Xq0jzoPa/g_L8jNgO.php and +4479372xxxxx.
The IMEI of the phone is used as an identifier by the C&C server. Other information sent there includes phone number, device serial number, phone model, carrier, and OS version.
Of note: Pincer checks to see if it’s being run in an emulator by checking the IMEI, phone number, operator, and phone model. (A common “anti-analysis” technique used by Windows malware.)
SHA1: 2157fd7254210ef2e8b09493d0e1be3b70d6ce69
Additional similar samples:
• 9416551d3965d3918eef3788b0377963d7b77032
• 1ebfc6f1f3e15773f23083c9d8d54771e28f5680
And on a final note…
The trojan includes a class called USSDDumbExtendedNetworkService. The URI_AUTHORITY variable is set to [redacted].com — and the redacted word is either associated with a French Canadian concrete company or else it may be the Twitter handle of a young Russian whose Google+ page lists employment as “Android developer”.
We don’t have any “concrete” evidence… but we’re pretty sure Pincer doesn’t have anything to do with Canada.
—————
Technical analysis by — Mikko Suominen
On 05/04/13 At 06:31 PM
Read more: Trojan:Android/Pincer.A