Twitter’s 2FA: SMS Double-Duty
Twitter introduced multi-factor login verification on Wednesday. Good news? Well… that depends.
Twitter’s initial implementation of two-factor authentication (2FA) relies on SMS.
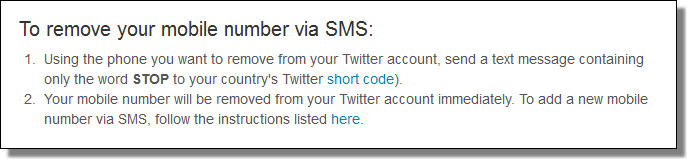
But… Twitter also uses SMS as a way to send and receive Tweets (making use of SMS for double-duty: social and security). It’s possible to “STOP” incoming Tweets via SMS, and that makes sense, because people sometimes end up roaming unexpectedly — and there needs to be a way to stop the SMS feature. Otherwise it could generate a costly bill.
Unfortunately, an attacker could use SMS spoofing to disable 2FA if he knows the target’s phone number.
We’ve done some testing.
The STOP command removes the phone number from the account — and that in turn disables Twitter’s 2FA.
Not great.
But there’s an even worse possibility at the moment.
If you don’t yet have 2FA enabled, an attacker who gains access to your account via spear phishing could enable it for himself!
All that’s required is random phone number and SMS spoofing the word “GO”.
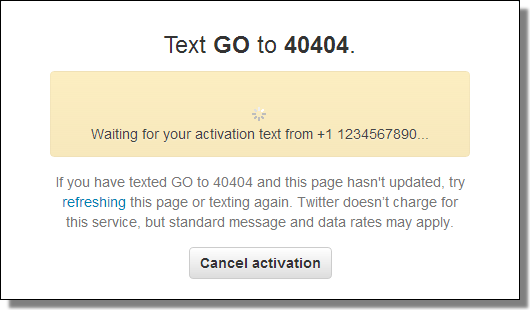
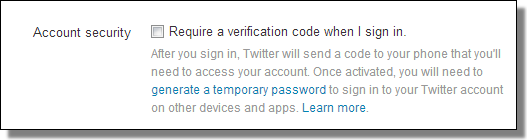
Then the attacker can enable the account’s 2FA.
Then send a message. (The message doesn’t contain a confirmation code, so it isn’t really needed.)
And then click “Yes”.
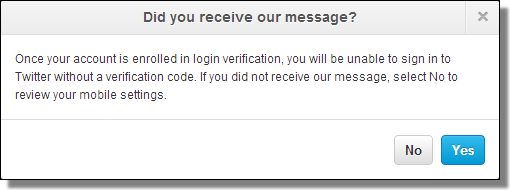
That’s it.
No confirmation code is needed to add a number. (Confirmation is required to change the account’s associated e-mail address.)
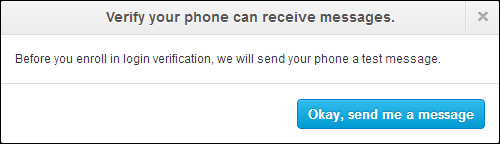
This is what the victim will see — even if they reset the account’s password.
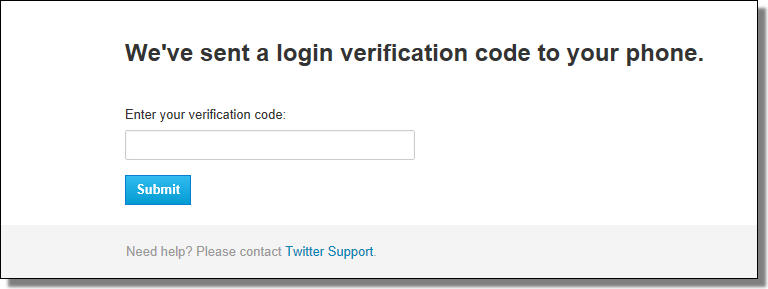
The victim will be locked out, and cannot recover the account without Twitter’s support.
So… perhaps you should enable your account’s 2FA — before somebody else does it for you.
Fortunately, the majority of Twitter users aren’t big targets. Unfortunately, accounts such as @AP are. And Twitter’s SMS-based 2FA could be more harm than help when the use case is a dedicated attacker.
Twitter’s blog post says “this feature has cleared the way for us to deliver more account security enhancements in the future.”
Let’s hope so.
On 24/05/13 At 12:40 PM
Read more: Twitter’s 2FA: SMS Double-Duty