How much money did GameOver ZeuS steal?
Wanted by the FBI: Evgeniy Mikhailovich Bogachev a.k.a. “slavik”.
Finally… a face and a name to go with an infamous alias.
Yesterday, the FBI announced a multi-national effort against the operator of GameOver ZeuS (GOZ), a notorious banking trojan.
We’ve been waiting for this:
Details here: GameOver Zeus Botnet Disrupted
Today we’ve been (eagerly) going through the associated documents — and the costs attributed to GOZ are very striking.
Examples of GameOver victims:
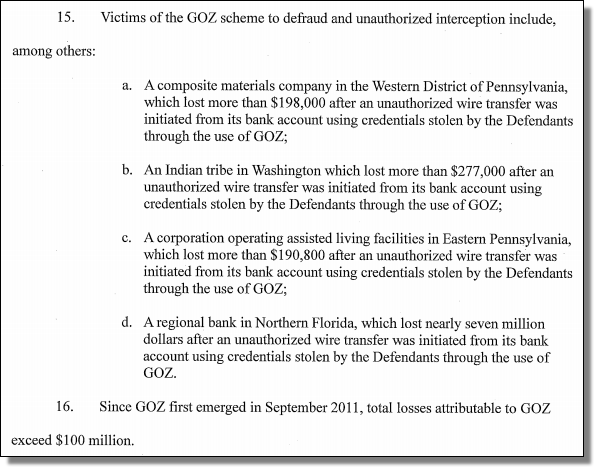
SEVEN MILLION dollars from one Florida bank? Wow.
Examples of CryptoLocker (ransomware dropped by GOZ) victims:
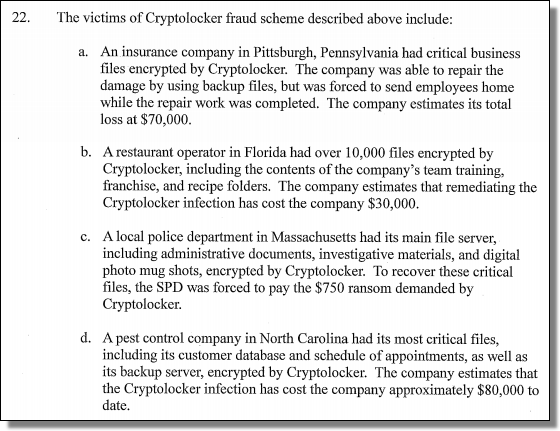
A restaurant in Florida had its recipes encrypted?
Now THAT is some “secret sauce”!
$30,000 in damage is really a significant cost for such a business.
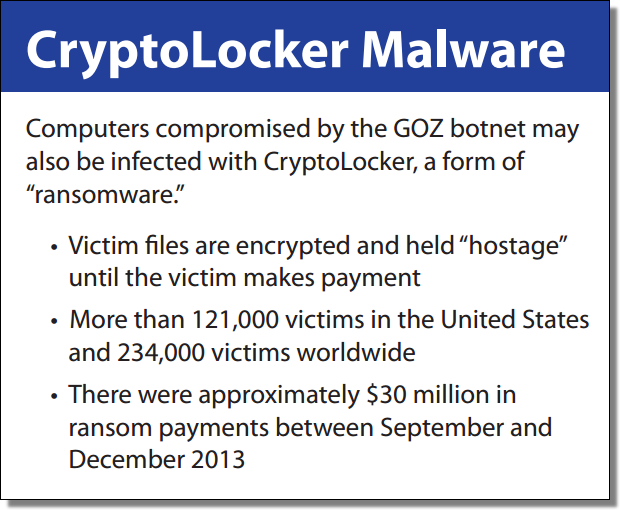
According to this FBI graphic, CryptoLocker made $30 million in payments during the last four months of 2013:
So here’s the thing about GOZ… it’s a peer-to-peer botnet and is highly resistant to “takedowns”. Law enforcement action is currently blocking critical command and control infrastructure — but it could be only a matter of time before slavik regains ownership via side channels. In the meanwhile, remediation efforts are underway. IP addresses related to GOZ are being directed to removal tools.
Our own (free) Online Scanner is listed in US-CERT’s Alert (TA14-150A).
There’s already a sizable increase in the number of scans performed according to our metrics.
Spread the word, and with any luck, the GameOver botnet will implode.
On 03/06/14 At 02:12 PM
Read more: How much money did GameOver ZeuS steal?
