How to test and exploit HTTP Parameter Pollution
There are two types of HPP attacks, the first one is Client-side Parameter Pollution vulnerability (which I will be explaining today) and the other one is Server-side Parameter Pollution vulnerability which will be discussed some other day.
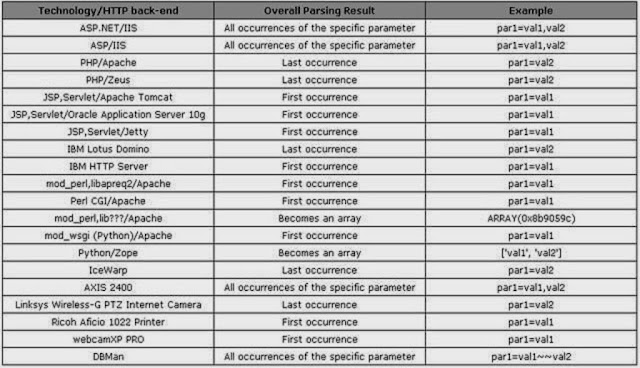
Submission of one parameter more than once is allowed by the HTTP protocol, the way through which the value of parameter is manipulated depends on the web technology used. Some parse the first or the last occurrence of the parameter, some parse the whole input and some of them create array of all the parameter. The above picture show how the values of the same parameter are parsed on different web technologies at server side.
Client-side Parameter Pollution
In client-side parameter pollution, the user is affected which leads to the trigger of a malicious action without the knowledge of the affected user. I will be explaining you the vulnerability with an easy to understand example, so here we go.
For example we will be considering a web application which allows users to caste their votes for their favorite candidate. The parameter used in the web application is votepoll_id which identifies the candidate for which the user is voting for. Based on the value of the parameter, application generates a page which include one link for each candidate.
The following code illustrates a voting page with the link of two candidates, where the user can caste his/her vote by clicking on the desired link.
URL : http://host/election.js?votepoll_id=0756
Link 1 : <a href =”vote.jsp?votepoll_id=0756&candidate=Alex”>Vote for Alex</a>
Link 2 : <a href =”vote.jsp?votepoll_id=0756&candidate=Max”>Vote for Max</a>
Suppose Sam, a supporter of Alex wants to vote for him, and thinks of subverting the results and realizes that the application is not properly sanitizing the value present in votepoll_id. So, therefore Sam exploits the HPP vulnerability to inject other parameter of his choice and sends it to Donna.
URL : http://host/election.js?votepoll_id=0756%26candidate%3DAlex
Here what Sam does is, he pollutes the votepoll_id parameter to inject another parameter of his choice which in our case is candidate=Alex pair.
By clicking on this link, Donna is redirected to the original website where she can caste her vote for the election. When Donna visits the page, malicious candidate value is injected in the URL.
URL : http://host/election.js?votepoll_id=0756%26candidate%3DAlex
Link 1 : <a href =”vote.jsp?votepoll_id=0756&candidate=Alex&candidate=Alex”>Vote for Alex</a>
Link 2 : <a href =”vote.jsp?votepoll_id=0756&candidate=Alex&candidate=Max>Vote for Max</a>
No matter which of the above link Donna clicks on, the application will receive two same parameters but which different values, the value of the parameter present first will be ONLY taken into consideration, and the value of second parameter will be IGNORED.
So from the above example, we an conclude that due to improper sanitization of the values, this vulnerability occurs. The developer expected to receive only one value i.e. only one candidate name so he provided basic java functionality which sadly resulted in HTTP Parameter Pollution attack.
Solutions for HPP attacks
-> URL encoding should be performed
-> Strict regular expression must be used
-> Should be aware of multiple occurrence of a parameter
About the Author : This post is written by Almas Malik, he blogs about Hacking and Cyber Security on his blog HaCking-SeC
Read more: How to test and exploit HTTP Parameter Pollution